Welcome to my weekly cybersecurity roundup! Here, I share updates on the projects I’m currently working on, along with the most insightful cybersecurity videos I watched, articles I found valuable, and podcasts I tuned into this week.
Featured Analysis
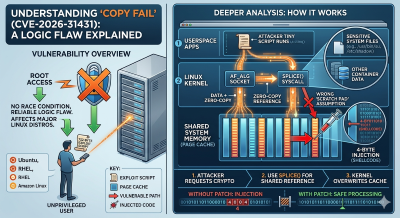
Understanding the “Copy Fail” Bug: A 732-Byte Path to Root
The “Copy Fail” vulnerability (CVE-2026-31431) is a critical security flaw recently discovered in the Linux kernel. Unlike many famous exploits that rely on “race conditions” (where an attacker has to get lucky with perfect timing), this bug is based on a pure logic error. This means it works almost 100% of the time. Using a tiny script, smaller than a standard text document, regular user with no special permissions can instantly become root, the “super-user” of a system. This vulnerability has been found to affect nearly every major version of Linux, including Ubuntu and Red Hat, making it a massive concern for security teams.
To understand the deeper technical breakdown, you have to look at how Linux handles memory. The kernel uses a feature called the page cache to store copies of files in RAM so they open faster. The “Copy Fail” bug happens because of a mistake in how the kernel processes encrypted data. When an attacker sends a specific command to the kernel’s “crypto” department, the kernel tries to be efficient by using a “zero-copy” method, which points directly to that shared memory (the page cache). Because of a coding error, the kernel thinks it is writing to a temporary “scratch pad” area, but it is actually writing four bytes of data directly into a sensitive file stored in memory, like the /usr/bin/su program used for logging in.
The danger here is stealth. Because the exploit only modifies the version of the file sitting in the computer’s RAM (the page cache) and doesn’t change the actual file stored on the hard drive, standard “file integrity” scanners might not see anything wrong. If an attacker injects their own code into the memory of a login program, they can bypass passwords entirely. This bug is also a major threat to cloud environments; an attacker could use it to “break out” of a container and take over the entire physical server. The best defense is to update the Linux kernel to version 6.12 or higher immediately, or temporarily disable the algif_aead module if a reboot isn’t possible.
Projects
- TryHackMe – Cloud Security Pitfalls – Complete
- TryHackMe – Enumeration & Brute Force – Complete
- TryHackMe – Session Management – In Progress
Videos
Articles
- ShinyHunters claim they have cruise giant Carnival’s booty as 7.5M emails surface – Leak-site bragging meets breach hunters as Have I Been Pwned flags millions of records
- Critical bug in CrowdStrike LogScale let attackers access files – CrowdStrike fixed CVE-2026-40050 in LogScale self-hosted, a critical flaw allowing unauthenticated file access via path traversal.
- Pre-Stuxnet Sabotage Malware ‘Fast16’ Linked to US-Iran Cyber Tensions – It targeted high-precision calculation software to tamper with results and packed a self-propagation mechanism.
- NASA Employees Duped in Chinese Phishing Scheme Targeting U.S. Defense Software – The Office of Inspector General (OIG) of the U.S. National Aeronautics and Space Administration (NASA) has revealed how a Chinese national posed as a U.S. researcher as part of a spear-phishing campaign to obtain sensitive information from the space agency, as well as from government entities, universities, and private companies, in violation of export control laws.
- ADT confirms data breach after ShinyHunters leak threat – Home security giant ADT has confirmed a data breach after the ShinyHunters extortion group threatened to leak stolen data unless a ransom is paid.
- Alleged Silk Typhoon hacker extradited to US for cyberespionage – A Chinese national accused of carrying out cyberespionage operations for China’s intelligence services has been extradited from Italy to the United States to face criminal charges.
- Electric Motorcycles and Scooters Face Hacking Risks to Security and Rider Safety – Vulnerabilities in Zero Motorcycles electric motorcycles and Yadea electric scooters can pose physical security and safety risks.
- US reportedly charges Scattered Spider hacker arrested in Finland – A 19-year-old dual United States and Estonian citizen arrested in Finland earlier this month faces federal charges in the U.S. alleging he was a prolific member of the notorious Scattered Spider hacking collective.
- Vimeo Confirms User and Customer Data Breach – The ShinyHunters group is threatening to leak stolen files unless Vimeo agrees to pay a ransom.
- Have I Been Pwned claims Pitney Bowes hit by 8.2M email address leak – Names, phone numbers, physical addresses also included in Shiny Hunters alleged data dump
- Hackers arrested for hijacking and selling 610,000 Roblox accounts – The Ukrainian police have arrested three individuals who hacked more than 610,000 Roblox gaming accounts and sold them for a profit of $225,000.
- Romanian leader of online swatting ring gets 4 years in prison – A Romanian national who led an online swatting ring that targeted more than 75 public officials, multiple journalists, and four religious institutions was sentenced to 4 years in federal prison.
- Two US Security Experts Sentenced to Prison for Helping Ransomware Gang – Ryan Goldberg of Georgia and Kevin Martin of Texas were each sentenced to four years in prison.
- China-Linked Hackers Target Asian Governments, NATO State, Journalists, and Activists – Cybersecurity researchers have disclosed details of a new China-aligned espionage campaign targeting government and defense sectors across South, East, and Southeast Asia, along with one European government belonging to NATO.
- 30,000 Facebook Accounts Hacked via Google AppSheet Phishing Campaign – A newly discovered Vietnamese-linked operation has been observed using a Google AppSheet as a “phishing relay” to distribute phishing emails with an aim to compromise Facebook accounts.
- Copy Fail: 732 Bytes to Root on Every Major Linux Distribution – Xint Code disclosed CVE-2026-31431, an authencesn scratch-write bug chaining AF_ALG + splice() into a 4-byte page cache write. A 732-byte PoC gets root on Ubuntu, Amazon Linux, RHEL, SUSE.