Welcome to my weekly cybersecurity roundup! Here, I share updates on the projects I’m currently working on, along with the most insightful cybersecurity videos I watched, articles I found valuable, and podcasts I tuned into this week.
Featured Analysis
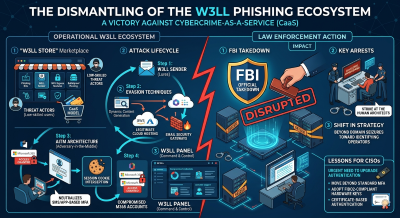
FBI Takedown of W3LL Phishing Service and Developer Arrest
The dismantling of the W3LL phishing ecosystem represents a significant victory in the ongoing battle against specialized cybercrime-as-a-service (CaaS) platforms. W3LL was not merely a simple phishing kit; it was a sophisticated, comprehensive suite designed specifically to bypass modern security controls, including multi-factor authentication (MFA). By utilizing an adversary-in-the-middle (AiTM) architecture, the W3LL Store enabled low-skilled threat actors to intercept session cookies in real-time. This effectively neutralized traditional SMS or app-based MFA, allowing unauthorized access to enterprise Microsoft 365 accounts without needing to crack complex passwords.
Technically, the W3LL toolkit was remarkable for its modularity and automation. It featured a custom “W3LL Panel” that managed the entire lifecycle of an attack. From the initial lure distribution via the “W3LL Sender” to the management of compromised credentials. The service employed advanced evasion techniques, such as dynamic content generation and the use of legitimate cloud hosting providers to mask malicious traffic. This level of operational security made it difficult for automated email security gateways to flag the URLs, as the infrastructure often sat behind trusted domains, leveraging the inherent reputation of major cloud providers to bypass blocklists.
The arrest of the developer in connection with the FBI takedown strikes a blow to the “industrialization” of phishing. Unlike generic malware, W3LL was a tailored business model that provided technical support, regular updates, and a marketplace for specialized tools. This enforcement action highlights a shift in federal strategy. Moving beyond simple domain seizures toward identifying and apprehending the human architects behind the code. For CISOs, this event underscores the urgent need to move beyond standard MFA toward FIDO2-compliant hardware keys or certificate-based authentication, as AiTM phishing continues to be the primary method for high-value account takeover.
Projects
- TryHackMe – Network Security Protocols – Complete
- TryHackMe – Intro to Cloud Security – In Progress
Videos
Articles
- FBI Recovers Deleted Signal Messages Through iPhone Notifications – Signal messages may persist in iPhone notification data, enabling FBI access even after deletion, a court case reveals.
- New Booking.com data breach forces reservation PIN resets – Booking.com has confirmed in a statement to BleepingComputer that hackers accessed some users’ data from booking information associated with their reservations.
- FBI takedown of W3LL phishing service leads to developer arrest – The FBI Atlanta Field Office and Indonesian authorities have dismantled the “W3LL” global phishing platform, seizing infrastructure and arresting the alleged developer in what is described as the first coordinated enforcement action between the United States and Indonesia targeting a phishing kit developer.
- 108 Malicious Chrome Extensions Steal Google and Telegram Data, Affecting 20,000 Users – Cybersecurity researchers have discovered a new campaign in which a cluster of 108 Google Chrome extensions has been found to communicate with the same command-and-control (C2) infrastructure with the goal of collecting user data and enabling browser-level abuse by injecting ads and arbitrary JavaScript code into every web page visited.
- Organizations Warned of Exploited Windows, Adobe Acrobat Vulnerabilities – The security defects allow attackers to escalate privileges and execute arbitrary code remotely.
- McGraw-Hill confirms data breach following extortion threat – Education company McGraw-Hill has confirmed in a statement to BleepingComputer that hackers exploited a Salesforce misconfiguration and accessed its internal data.
- Sweden Blames Pro-Russian Group for Cyberattack Last Year on Its Energy Infrastructure – In what was Sweden’s first public mention of the attack, the country’s minister for civil defense said it targeted a heating plant in western Sweden.
- US nationals behind DPRK IT worker ‘laptop farm’ sent to prison – Two U.S. nationals have been sent to prison for helping North Korean remote information technology (IT) workers to pose as U.S. residents and get hired by over 100 companies across the country, including many Fortune 500 firms.
- $10 Domain Could Have Handed Hackers 25k Endpoints, Including in OT and Gov Networks – Researchers found adware capable of killing cybersecurity products and pushing more dangerous payloads to infected systems.
- Man gets 30 months for selling thousands of hacked DraftKings accounts – 23-year-old Kamerin Stokes of Memphis, Tennessee, was sentenced to 30 months in prison for selling access to tens of thousands of hacked DraftKings accounts.
- Two North Korean IT Worker Scheme Facilitators Jailed in the US – Kejia Wang and Zhenxing Wang compromised the identities of dozens of US persons to help land jobs at over 100 companies.