Welcome to my weekly cybersecurity roundup! Here, I share updates on the projects I’m currently working on, along with the most insightful cybersecurity videos I watched, articles I found valuable, and podcasts I tuned into this week.
Featured Analysis
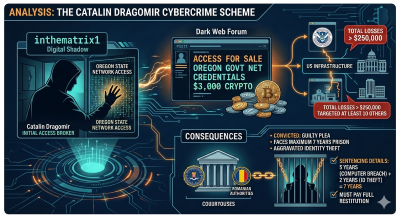
Featured article analysis: Romanian Hacker Pleads Guilty to Selling Access to US State Network
The SecurityWeek article details the guilty plea of Catalin Dragomir, a 45-year-old Romanian national, who admitted to selling unauthorized access to an Oregon state government network. Operating under the online handle “inthematrix1,” Dragomir was identified as a significant “initial access broker” within the cybercriminal underworld. In June 2021, he successfully breached the Oregon Department of Emergency Management and subsequently advertised administrative credentials for the network on a dark web forum. To prove the legitimacy of his access to potential buyers, he provided samples of sensitive personal identifying information (PII) belonging to state employees, including Social Security numbers and login credentials, eventually selling the access for approximately $3,000 in cryptocurrency.
The scope of Dragomir’s criminal activity extended well beyond a single state office, highlighting the systemic threat posed by access brokers to U.S. infrastructure. Federal prosecutors revealed that Dragomir targeted and sold access to at least 10 other victims across the United States, resulting in total financial losses estimated at over $250,000. These types of brokers serve as the “entry point” for more destructive cyberattacks, as the access they sell is frequently purchased by ransomware groups looking for a foothold in high-value targets. Following an international investigation involving the FBI and Romanian authorities, Dragomir was arrested in Romania in late 2024 and extradited to the U.S. in early 2025 to face justice.
The legal resolution of the case underscores the Department of Justice’s commitment to prosecuting international cybercriminals who target domestic government entities. Dragomir pleaded guilty to one count of obtaining information from a protected computer and one count of aggravated identity theft. He faces a maximum of seven years in federal prison. Consisting of a five-year term for the computer breach and a mandatory consecutive two-year sentence for identity theft; along with significant fines and a requirement to pay full restitution to his victims. Scheduled for sentencing in May 2026, the case serves as a stern warning regarding the legal consequences of cyber espionage and the persistent efforts of law enforcement to dismantle dark web marketplaces.
Projects
Videos
Articles
- PayPal Data Breach Led to Fraudulent Transactions – PayPal blamed an application error for the exposure of customer personal information for nearly 6 months.
- Romanian Hacker Pleads Guilty to Selling Access to US State Network – Catalin Dragomir admitted in a US court to selling access to an Oregon state government office’s network.
- Ukrainian Gets 5 Years in US Prison for Aiding North Korean IT Fraud – Oleksandr Didenko sold the stolen identities of US citizens, allowing North Koreans to get hired using freelance work platforms.
- The FBI Says These Wi-Fi Routers Are Unsafe, And Here’s Why
- Ad tech firm Optimizely confirms data breach after vishing attack – New York-based ad tech company Optimizely has notified an undisclosed number of customers of a data breach after threat actors compromised some of its systems in a voice phishing attack.
- Spain arrests suspected hacktivists for DDoSing govt sites – Spanish authorities have arrested four alleged members of a hacktivist group believed to have carried out cyberattacks targeting government ministries, political parties, and various public institutions.
- Anthropic Says Chinese AI Firms Used 16 Million Claude Queries to Copy Model – Anthropic on Monday said it identified “industrial-scale campaigns” mounted by three artificial intelligence (AI) companies, DeepSeek, Moonshot AI, and MiniMax, to illegally extract Claude’s capabilities to improve their own models.
- UK fines Reddit $19 million for using children’s data unlawfully – The UK Information Commissioner’s Office (ICO) has fined Reddit £14.47 million (over $19.5 million) for collecting and using the personal information of children under 13 without adequate safeguards.
- Hackers Hide Pulsar RAT Inside PNG Images in New NPM Supply Chain Attack – Cybersecurity researchers at Veracode reveal a typosquatting attack that disguises Pulsar RAT as images to bypass Windows security and antivirus programs.
- Threat Intelligence Has a Human-Shaped Blind Spot – How I realized what I was taught about threat intelligence was missing something crucial.
- Ex-L3Harris exec jailed for selling zero-days to Russian exploit broker – The former head of Trenchant, a specialized U.S. defense contractor unit, was sentenced Tuesday to more than seven years in federal prison for stealing and selling zero-day exploits to a Russian broker whose clients include the Russian government.
- Wynn Resorts Confirms Data Breach After Hackers Remove It From Leak Site – The high-end casino and hotel operator has admitted that employee data was stolen by ShinyHunters.
- Google Disrupts Chinese Cyberespionage Campaign Targeting Telecoms, Governments – The UNC2814 threat actor has been active since at least 2017, targeting organizations across 42 countries.
- Ransomware payment rate drops to record low as attacks surge – The number of ransomware victims paying threat actors has dropped to 28% last year, an all-time low, despite a significant increase in the number of claimed attacks.
- New AirSnitch attack breaks Wi-Fi encryption in homes, offices, and enterprises – That guest network you set up for your neighbors may not be as secure as you think.
- Ukrainian man pleads guilty to running AI-powered fake ID site – A Ukrainian man has pleaded guilty to operating OnlyFake, an AI-powered website that generated and sold more than 10,000 photos of fake identification documents to customers worldwide.
- APT37 hackers use new malware to breach air-gapped networks – North Korean hackers are deploying newly uncovered tools to move data between internet-connected and air-gapped systems, spread via removable drives, and conduct covert surveillance.