Welcome to my weekly cybersecurity roundup! Here, I share updates on the projects I’m currently working on, along with the most insightful cybersecurity videos I watched, articles I found valuable, and podcasts I tuned into this week.
Featured Analysis
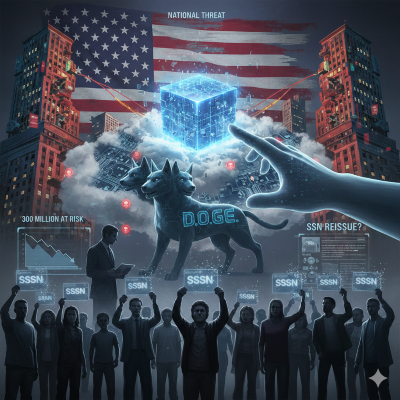
Featured article analysis: All U.S. Social Security numbers may need to be changed following a massive breach that is already being investigated as a national threat
The provided article from Ecoticias details a alarming security crisis involving the potential exposure of Social Security numbers (SSNs) for nearly every American citizen. The analysis below examines the core allegations, the institutional risks involved, and the unprecedented proposed solution.
The article centers on a whistleblower disclosure from Chuck Borges, the former Chief Data Officer at the Social Security Administration (SSA). Borges alleges that a federal tech group known as the Department of Government Efficiency (DOGE) created a “live copy” of the government’s master Social Security database on a cloud system that lacked standard security oversight and bypassed established legal restrictions. According to Borges, this maneuver effectively moved sensitive personal data: including names, birth dates, and citizenship status for over 300 million people, out of highly monitored internal systems and into a more vulnerable environment where access was less transparent.
From an institutional perspective, the situation represents a profound breakdown in data governance and national security. While the SSA has maintained that its core internal databases remain secure and uncompromised, the whistleblower suggests that the existence of a secondary, less-guarded copy creates a permanent “hidden risk” for the entire population. The article highlights the tension between modernizing government tech infrastructure and maintaining the rigid security protocols required for “crown jewel” datasets. If the allegations are accurate, the breach of such a comprehensive database could empower bad actors to perpetrate fraud against nearly every government and financial system in existence.
The most striking takeaway from the analysis is the radical remedy being considered: the wholesale reissuance of Social Security numbers for all Americans. Historically, SSNs are permanent identifiers that are rarely changed except in extreme cases of individual identity theft. However, because the alleged exposure is so vast and the data, such as parents’ names and birthplaces is immutable, experts warn that the current system may be fundamentally broken. Reissuing hundreds of millions of numbers would be an administrative undertaking of unprecedented scale, yet it is increasingly framed as a necessary step to mitigate a lifelong threat of identity fraud and national economic instability.
Projects
- TryHackMe – OWASP Top 10 2025: IAAA Failures – Complete
- TryHackMe – SOC Role in Blue Team – In Progress
Articles
- All U.S. Social Security numbers may need to be changed following a massive breach that is already being investigated as a national threat
- Man arrested for demanding reward after accidental police data leak – Dutch authorities arrested a 40-year-old man after he downloaded confidential documents that had been mistakenly shared by the police and refused to delete them unless he received “something in return.”
- Study Uncovers 25 Password Recovery Attacks in Major Cloud Password Managers – A new study has found that multiple cloud-based password managers, including Bitwarden, Dashlane, and LastPass, are susceptible to password recovery attacks under certain conditions.
- OpenClaw threats: assessing the risks, and how to handle shadow AI – What corporate security teams should do about the “viral” AI agent.
- CIA makes new push to recruit Chinese military officers as informants – Just weeks after a dramatic purge of China’s top general, the CIA is moving to capitalize on any resulting discord with a new public video targeting potential informants in the Chinese military.
- Microsoft says bug causes Copilot to summarize confidential emails – Microsoft says a Microsoft 365 Copilot bug has been causing the AI assistant to summarize confidential emails since late January, bypassing data loss prevention (DLP) policies that organizations rely on to protect sensitive information.
- Ivanti Exploitation Surges as Zero-Day Attacks Traced Back to July 2025 – Security researchers have seen the vulnerabilities being exploited to deliver shells, conduct reconnaissance, and download malware.
- Texas sues TP-Link over Chinese hacking risks, user deception – Texas sued networking giant TP-Link Systems, accusing the company of deceptively marketing its routers as secure while allowing Chinese state-backed hackers to exploit firmware vulnerabilities and access users’ devices.
- Nigerian man gets eight years in prison for hacking tax firms – A Nigerian national was sentenced to eight years in prison for hacking multiple tax preparation firms in Massachusetts and filing fraudulent tax returns seeking over $8.1 million in refunds.
- California Man Found Guilty of Defrauding His Former Employer Optum, Inc. – United States Attorney Daniel N. Rosen announced today that Karan Gupta, age 47, was found guilty yesterday of one count of conspiracy to commit wire fraud, ten counts of wire fraud, and one count of money laundering conspiracy, following a six-day jury trial in U.S. District Court in Minneapolis before U.S. District Court Judge Kate M. Menendez.
- Ukrainian gets 5 years for helping North Koreans infiltrate US firms – A Ukrainian national was sentenced to five years in prison for providing North Korean IT workers with stolen identities that helped them infiltrate U.S. companies.
- PayPal discloses data breach that exposed user info for 6 months PayPal is notifying customers of a data breach after a software error in a loan application exposed their sensitive personal information, including Social Security numbers, for nearly 6 months last year.