In the News
-
What’s New in Cybersecurity This Week: Projects, Videos, Articles & Podcasts I’m Following – 4/13/26
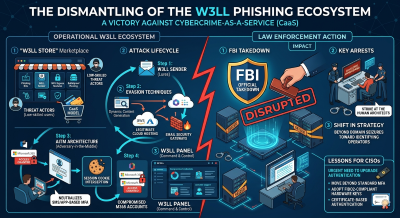
Welcome to my weekly cybersecurity roundup! Here, I share updates on the projects I’m currently working on, along with the most insightful cybersecurity videos I watched, articles I found valuable, and podcasts I tuned into this week. Featured Analysis FBI Takedown of W3LL Phishing Service and Developer Arrest The dismantling of the W3LL phishing ecosystem
-
What’s New in Cybersecurity This Week: Projects, Videos, Articles & Podcasts I’m Following – 4/6/26
Welcome to my weekly cybersecurity roundup! Here, I share updates on the projects I’m currently working on, along with the most insightful cybersecurity videos I watched, articles I found valuable, and podcasts I tuned into this week. Featured Analysis Iran-linked Hackers Disrupt U.S. Critical Infrastructure via PLC Attacks / 4,000 U.S. Industrial Devices Exposed. The
-
What’s New in Cybersecurity This Week: Projects, Videos, Articles & Podcasts I’m Following – 3/30/26
Welcome to my weekly cybersecurity roundup! Here, I share updates on the projects I’m currently working on, along with the most insightful cybersecurity videos I watched, articles I found valuable, and podcasts I tuned into this week. Featured Analysis The Axios NPM Supply Chain Attack and its Attribution to State-Sponsored Actors The recent alert from
-
What’s New in Cybersecurity This Week: Projects, Videos, Articles & Podcasts I’m Following – 3/23/26
Welcome to my weekly cybersecurity roundup! Here, I share updates on the projects I’m currently working on, along with the most insightful cybersecurity videos I watched, articles I found valuable, and podcasts I tuned into this week. Featured Analysis FBI Warns of Russian Intelligence Targeting Signal Messenger via Sophisticated Phishing and Zero-Day Exploits. The recent
-
What’s New in Cybersecurity This Week: Projects, Videos, Articles & Podcasts I’m Following – 3/16/26
Welcome to my weekly cybersecurity roundup! Here, I share updates on the projects I’m currently working on, along with the most insightful cybersecurity videos I watched, articles I found valuable, and podcasts I tuned into this week. Featured Analysis Hack Attempt Reported at Poland’s Nuclear Research Center (National Centre for Nuclear Research – NCBJ) The
-
What’s New in Cybersecurity This Week: Projects, Videos, Articles & Podcasts I’m Following – 3/2/26
Welcome to my weekly cybersecurity roundup! Here, I share updates on the projects I’m currently working on, along with the most insightful cybersecurity videos I watched, articles I found valuable, and podcasts I tuned into this week. Featured Analysis Featured article analysis: FBI investigating hack on its wiretap and surveillance systems: Report The reported hack
-
What’s New in Cybersecurity This Week: Projects, Videos, Articles & Podcasts I’m Following – 2/9/26
Welcome to my weekly cybersecurity roundup! Here, I share updates on the projects I’m currently working on, along with the most insightful cybersecurity videos I watched, articles I found valuable, and podcasts I tuned into this week. Featured Analysis Featured article analysis: The Rise of OpenClaw: AI with Hands OpenClaw, formerly known as Clawdbot and Moltbot,